Jan 2022
Metaverse– The term indicates “Meta + Universe = Metaverse”
We are listening and have the questions in our mind – “What is Metaverse? What can happen with the introduction of Metaverse and Decentralization of the Internet together?”
The diverse forms of technology such as applications, user-generated content, hardware, Cloud Infrastructure, software tools, platforms will form an alliance to drive the metaverse. The metaverse will include various user experiences including, but not limited to, entertainment, gaming, commerce, social interactions, education, and research. Managed IT service providers in India will get a good opportunity to grow with the evolution of Internet (Web 3.0) and Metaverse as they will get a decentralized and virtual platform to manage, or modify or control.
Data Scientists/Researchers believe that the metaverse is a decentralized virtual world, not controlled by any one corporation or reliant on one company’s hardware, built on open standards so anyone can access it (like the internet). This can be a part of Metaverse not the complete version of Metaverse.
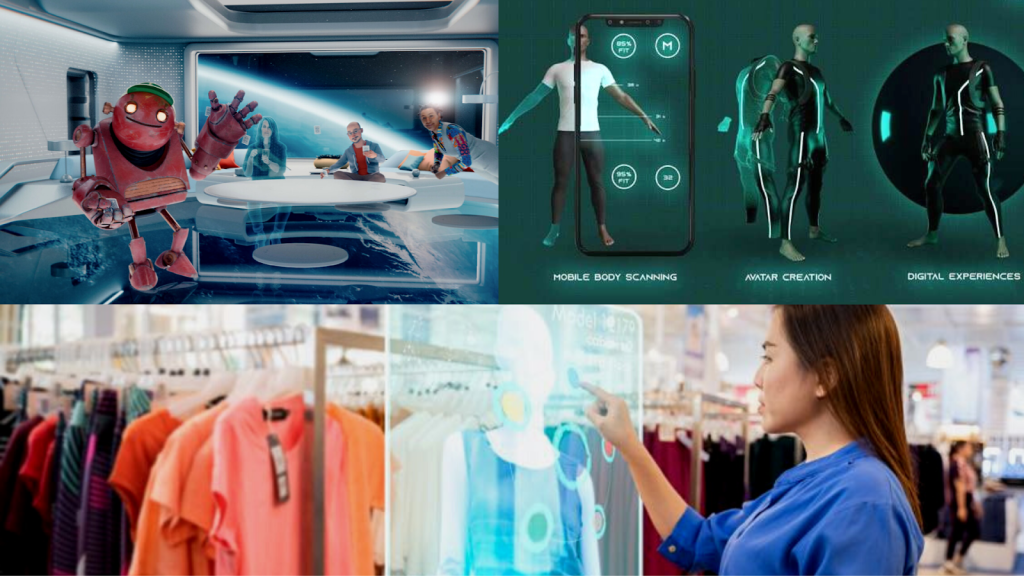
Yes, There will be Artificial intelligence combined with machine learning and other technologies to produce the 3D version of Robots or virtual reality platforms.
- There will be virtual robots doing meetings with employees like us.
- Shopping with Augmented reality and more.
Metaverse is a virtual reality platform in anything and everything you can imagine. If the metaverse really is to be the next generation of the web, Tech Giants and other researchers need serious commitment and action now to ensure it is built to prioritize the rights, safety, and well-being of everyone.
Impact and the role of IT managed service providers in India
Privacy: Virtual reality and augmented reality hardware, the tools of this new digital world, vastly expands the data tech companies can collect, including everything from your location to your heart rate and the movements of your eyes and fingers. Without a concerted focus on data protection, the metaverse will become another space where users’ data is being exploited for financial gain or other benefits. Much of the world still lacks fit-for-purpose data privacy laws, and soon Metaverse can be a nightmare. In today’s digital age, companies can become victims of cyberattack easily. With Metaverse, hackers will try to intrude in this virtual reality platform to steal the data of the user. Managed IT service provider (MSPs) layers your network with the latest hardware and software designed to keep cyber threats at bay. From anti-malware and anti-ransomware to the latest firewalls and phishing mitigation software, MSP’s will help tech giants to keep their data safe. For 2021, the managed services segment registered the highest growth rate at 7.2 per cent, followed by project-oriented services at 6.3 per cent, and support services at 5.3 per cent. As India is known to be one of the most reliable managed service providers in the world, there is a huge opportunity to grow with the evolution of Metaverse.
Preventing abuse: Given the immersive, persistent nature of the metaverse, there is good reason to believe that online abuse in these spaces will be an even greater danger. Abuse in virtual reality is far more traumatic than in other digital worlds because virtual reality has the power to blur the line between ethics/humanity and what’s not. MSP’s can control the environment or build software to protect users from any abuse in virtual reality platforms.
Common Interface/ Common Standards: There should be no one single metaverse — but rather many metaverses and there can be multiple access points. India holds a strong position in Managed IT services, whether being a cloud service provider or IT infrastructure management services. Tech Giants can provide control/access or manage the metaverses by different MSP’s . We need common standards and interoperability to bridge between these spaces, so that they can be accessed by other users/companies or modified or aborted. So that we don’t end up creating a virtual space where we cannot travel seamlessly or can modify or control it.
There is a long way to go to develop the technologies to make this work, but if successful, it could be a far more exciting digital future. If the metaverse is going to be the next step in the web’s evolution, we have to make sure we cover all its consequences before creating it and enable different common points of control for complete access to the metaverse. Managed Service Providers are keeping an eye on the latest technologies and methods to prepare themselves for the next generation of Internet.